Privacy By Design Training
LMS Packages
Pre-made courses that integrate with your organization’s Learning Management System
Privacy shouldn’t be restricted to the privacy office.
Everyone within the organization can benefit from a better understanding. From your developers to your C-suite, from Human Resources to Marketing. From your architects to your product managers. Even if you have an army of privacy engineers and privacy analyst, they can benefit from an improved understanding of the concepts pertinent to privacy. We offer a range of learning and growth areas for every level and depth of knowledge!
Legal Compliance Style Courses Are Dry and Unimpactful...
Learning should be fun, interesting and insightful! Our courses are mostly developed as self-contained modules that can be installed in your company’s learning management system to make available on-demand for your employees and contractors, either as required learning or for those looking to improve their knowledge and skills. Our course often starts off at a high level with detail and depth available for learners wanted a better understanding.
LMS Based Courses
are available around the world!
can be self-paced based on the learner’s availability and learning speed, and
don’t have to be done at a specific time, meaning your global workforce can learn in their preferred time zone.

Subject Domains
Privacy Design
Target Audience: Privacy Engineers and other Privacy Professionals, Software Developers, Managers, Architects and Engineers.
D100 and D101 courses suitable for all audiences.
Engineering
Target Audience: Software Architects, Product Designers, Software Engineers, Product Managers, Security Engineers, Privacy Engineers and other Technologists, Database designers and architects
UI/UX
Target Audience: Marketing, Product Designers, UI/UX, Front-End Developers, Interface Designers, Product Managers, Privacy Professionals
Privacy Design
D100 – Introduction
By completing this lesson, participants should understand some of the common risks to customer privacy and business operation seen in manipulative designs.
D111 – Privacy Design Strategies
Upon completion of this course, students should understand how to implement privacy by design in a reliable and concrete way, using up to eight common strategies and 26 specific tactics.
D121 – Threat Modeling
Upon completion of this course, students should understand the relationship between threats and risks, identify threat actors, at-risk individuals, and proxies, and distinguish between normative and tangible harms.
D131 – Privacy Risk
Upon completion of this course, students should understand the basics of the Factors Analysis of Information Risk (FAIR) methodology and its application to privacy risk assessment, as well as the value of using quantitative measures in a privacy risk context.
D101 – Privacy Harms
This lesson provides an introduction into identifying privacy harms. Afterwards, participants should be able to properly identify potential areas of concern for privacy.
D211 – Design Process
Upon completion of this course, students should understand the key questions to ask during the design process in order to ensure that privacy considerations are prioritized and privacy concerns are addressed.
D221 – Proxies and Agents
Learn the overarching process of approaching design with privacy in mind.
D231 – Mitigating Risks
Upon completion of this course, students should understand the relationship between the Hoepman Privacy Design Strategies and the Factors Analysis of Information Risk (FAIR) model, how to apply the controls described in the former to the risks described in the latter, and how to use these controls to approach a threat landscape.
D201 – Models of Privacy Norms
This lesson extends the privacy harms to discuss other models of privacy norms beyond Solove.

Did You Know?
The full suite of Design courses are available as part of our Professional Development course offered multiple times a year?
D321 – Diagramming Threats
Upon completion of this course, students should understand how to use online tools to systematically map out the interactions and relationships between threat actors, at-risk individuals, and others, and produce a practical threat model diagram.
D331 – Quantitative Risk Assessment
Dive deeper than D131 in quantifying privacy risks, comparing pre and post control risks, and assessing organizational risk tolerance.
Engineering
E101 – Hashing
One-way functions provide numerous privacy protections. This lesson discusses some of the use cases for hashing as well as common pitfalls.

E111 – Privacy Architecture
Privacy architecture looks to reduce privacy risks through decentralization and de-identification of data.
E121 – Privacy Enhancing Technologies
PETs are a set of technologies which have a primary purpose of preserving or enhancing privacy. This lesson covers the basics of the most popular PETs in use.
E131 – Anonymization, Pseudonymization & De-Identification
This lesson covers the syntactic
dataset measures of anonymity
and their proper use.
E201 – Fuzzy Hashing
Hashing can be very unforgiving. Fuzzing hashing provides a way of preserving privacy while allowing for some flexibility.
E211 – Technical Policy Enforcement
This lesson covers various techniques to technically enforce policies in systems.
E221 – Differential Privacy
An introductory lesson into how differential privacy works and its potential applications.

E231 – Deidentification Techniques
Here we examine the three major techniques for data deidentification including suppression, generalization and noise as well as pitfalls to watch out for such as overlapping.
E202 – Translucent Databases
Often times database needs to be accessible to some, like administrators, who don’t need the underlying data. Translucent database provide protection.

Did You Know?
The full suite of Design courses are available as part of our Professional Development course offered multiple times a year?

E222 – Secure Multi- Party Computation
An introductory lesson into how Secure Multi-Party Computation works and its potential applications.
UI/UX
U111 – Data Minimization
Upon completion of this course, students should understand why data increases risk, the specific issues surrounding the collection of data, and how to avoid unnecessary data risks through data minimization.
U121 – Understanding Consent
Upon completion of this course, students should understand what to look for when assessing the validity of consent, and where consent is required.

U131 – Deceptive Designs
Upon completion of this course, students should be able to state the common factors that contribute to manipulative interfaces. They should also be able to avoid manipulation and coercion in their own designs.

U141 – Privacy Notice Design Space
Upon completion of this course, students should understand the key considerations and various options involved in crafting a well-designed privacy notice.
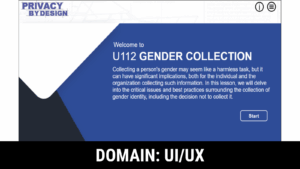
U112 – Gender Collection
Upon completion of this lesson, you will have a comprehensive understanding of the complexities surrounding gender collection and how to navigate them effectively.

Did You Know?
The full suite of Design courses are available as part of our Professional Development course offered multiple times a year?
Our Pricing
Organization Licenses
Small (3-99)
$375
$2,500
$3,750
Medium (100-999)
$1,500
$10,000
$15,000
Large (1,000-9,999)
$4,500
$30,000
$45,000
Enterprise (>10,000)
$9,000
$60,000
$90,000
Includes
1 Year License
1 Year License
1 Year License

Add general privacy awareness lessons from leading provider Teach Privacy. See Catalog.
N/A
Inclusive
You may select any of the TeachPrivacy courses as part of your 10 course selection
Contact to Add-On
TeachPrivacy courses must be added separately. Please note your interest in the order form.
Organizational prices based on no customization and training hosted on your internal company Learning Management Systems (LMS)
Ready to Order?
Information submitted for this form will be used to contact you and provide you with any requested services. Information will not be shared unless payment for services are required, in which case we will provide information to billing vendors for the purposes of invoicing and receiving payment. You will not be placed on any mailing list, nor will you information be shared for marketing purposes.
